Certified Information Security Manager ISACA

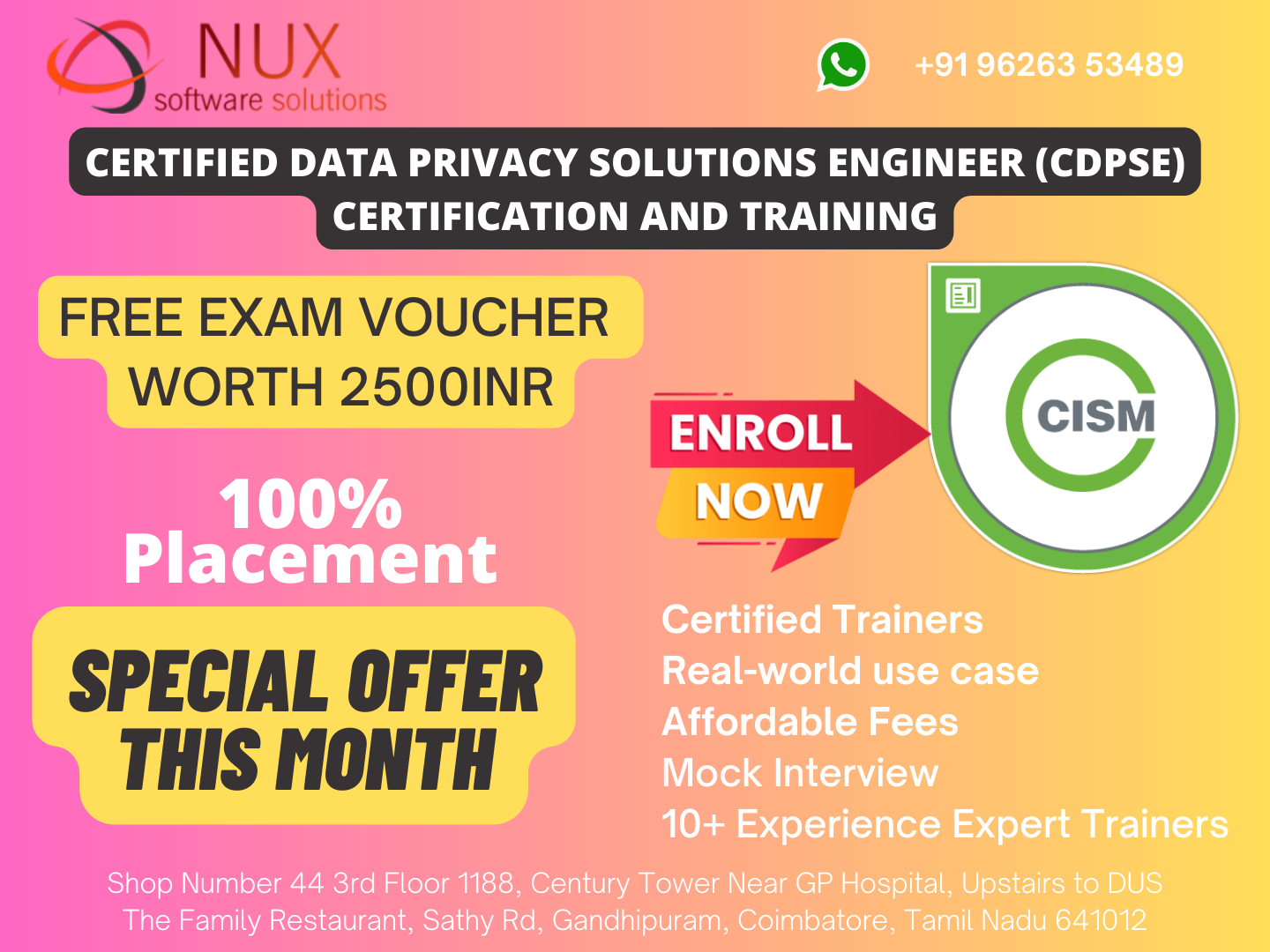
Best ISACA Information Security Governance training courses classes deliver by Nux software Training & Certification Solutions in coimbatore.
Nux software Training & Certification Solutions in Coimbatore is truly committed to providing a top-notch learning experience. The emphasis on advanced training programs, hands-on experience, expert trainers, and flexible training options, including live project and industrial training, makes it a promising choice for professionals seeking to enhance their skills.
The availability of a well-managed and accessible lab environment 24/7 suggests a commitment to practical learning, and the international expert trainers with real-time industry experience add credibility to the training programs. It’s great to know that they understand the needs of individuals and professionals, aiming to provide effective and cost-efficient training programs.
Get the best Training on ISACA from Nux software Training & Certification Solutions.
Do you want to learn more about ISACA? In that situation, Nux software Training & Certification Solutions would be an excellent choice. We provide a thorough ISACA training package in which you will be instructed on all elements of it.
To provide high-quality training, we have some of the top faculty and one of the best infrastructures. Our course is divided into sections in which students learn about many features of this programming language.
Course Syllabus
ISACA Information Security Governance Syllabus
A. Enterprise Governance
Organizational Culture
Legal, Regulatory, and Contractual Requirements
Organizational Structures, Roles, and Responsibilities
B. Information Security Strategy
Information Security Strategy Development
Information Governance Frameworks and Standards
Strategic Planning (e.g., budgets, resources, business case).
A. Information Security Risk Assessment
Emerging Risk and Threat Landscape
Vulnerability and Control Deficiency Analysis
Risk Assessment and Analysis
B. Information Security Risk Response
Risk Treatment / Risk Response Options
Risk and Control Ownership
Risk Monitoring and Reporting
A. Information Security Program Development
Information Security Program Resources (e.g., people, tools, technologies)
Information Asset Identification and Classification
Industry Standards and Frameworks for Information Security
Information Security Policies, Procedures, and Guidelines
Information Security Program Metrics
B. Information Security Program Management
Information Security Control Design and Selection
Information Security Control Implementation and Integrations
Information Security Control Testing and Evaluation
Information Security Awareness and Training/td>
Management of External Services (e.g., providers, suppliers, third parties, fourth parties)
Information Security Program Communications and Reporting
A. Incident Management Readiness
Incident Response Plan
Business Impact Analysis (BIA)
Business Continuity Plan (BCP)
Disaster Recovery Plan (DRP)
Incident Classification/Categorization
Incident Management Training, Testing, and Evaluation
B. Incident Management Operations
Incident Management Tools and Techniques
Incident Investigation and Evaluation
Incident Containment Methods
Incident Response Communications (e.g., reporting, notification, escalation)
Incident Eradication and Recovery
Post-incident Review Practices